Explore Nayaka's Blog
Discover insights, strategies, and the latest trends in cybersecurity and startups. Stay informed with expert perspectives to drive your business forward.
Drive Success with our Insights
Cybersecurity moves fast. Our blog cuts through the noise with practical guidance, emerging threat analysis, and real-world perspectives from the front line – so you stay ahead of what matters, not just informed about what happened.
Drive Success with our Insights
Our Posts
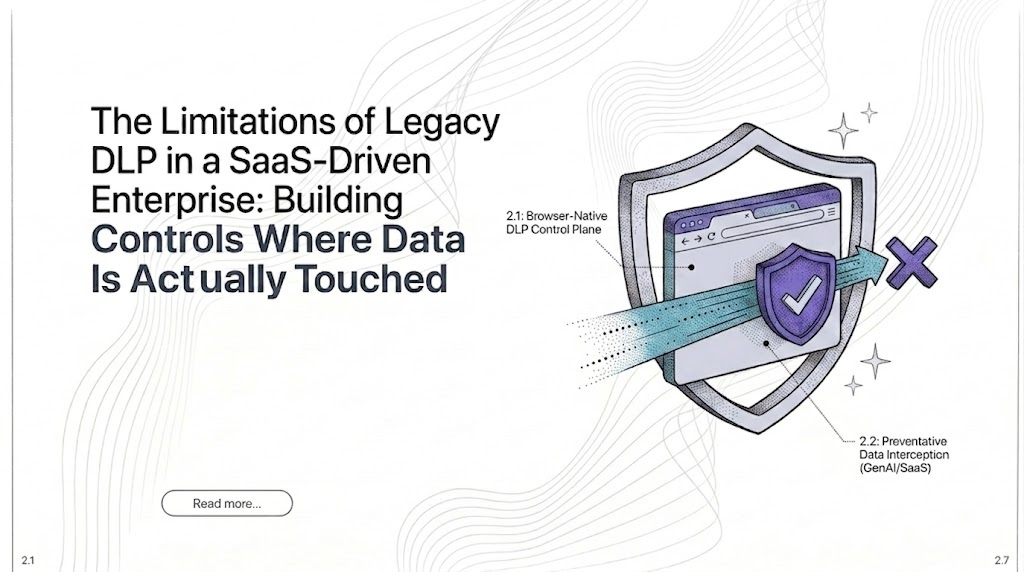
The Limitations of Legacy DLP in a SaaS-Driven Enterprise: Building Controls Where Data Is Actually Touched
Most organisations that have invested in data loss prevention believe they have the problem reasonably under control. Endpoint agents are deployed, network monitoring is in place, and policies govern how data moves across managed infrastructure. What many have not fully
Read More

Agentic AI Workflow Security: Why Existing Controls Fall Short and What Organisations Must Do Now
The security architecture most organisations rely on was designed around a straightforward assumption that systems execute instructions, and threats arrive from outside. A firewall blocks unauthorised traffic. An automated playbook follows a fixed sequence. An access policy grants or denies
Read More

Pairing Atlassian Guard with Metomic for Full Data Control
Read More

How Data-Driven Strategies Can Transform Your Sales Pipeline
Read More

Metomic as the Essential Data Control Layer
Metomic is the complementary data control layer that secures the sensitive data living inside your Confluence and Jira workspaces. Where Guard shows who accessed or changed what, Metomic shows what data was exposed, and how to fix it. Metomic fills
Read More

The Top 10 Security Challenges Keeping CISOs Awake
Read More