Next-Gen Honeypots
A cutting-edge deception platform lures attackers into a network of narrative-driven decoys, providing deep insights into their tactics, techniques, and procedures.
Most defences tell you when an attacker has already caused damage. Next-generation honeypots go further – drawing attackers into a deceptive environment, studying exactly how they operate, and alerting you to genuine intrusions with near-zero false positives.
Narrative-driven deception platform
Narrative-driven deception platform
Actionable threat intelligence
Comprehensive deception coverage,
backed by expert support
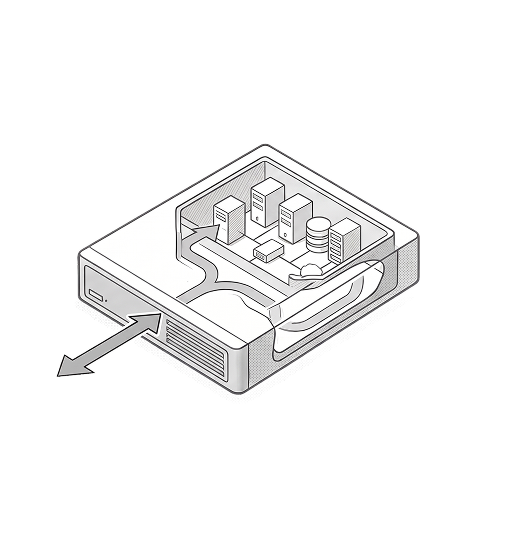
Perimeter defences keep attackers out – until they do not. Once someone is inside your environment, most tools only detect them after they have already moved laterally, escalated privileges, or exfiltrated data. Next-gen honeypots change the dynamic entirely. Strategically placed decoys that mirror real assets give attackers something convincing to target – while every action they take inside that deceptive environment is logged, analysed, and used to build a precise picture of their tactics before any real damage is done.
Nayaka helps mid-size organisations select and deploy the right deception platform from our partner ecosystem, with expert support from environment mapping through to live deployment and intelligence operationalisation.
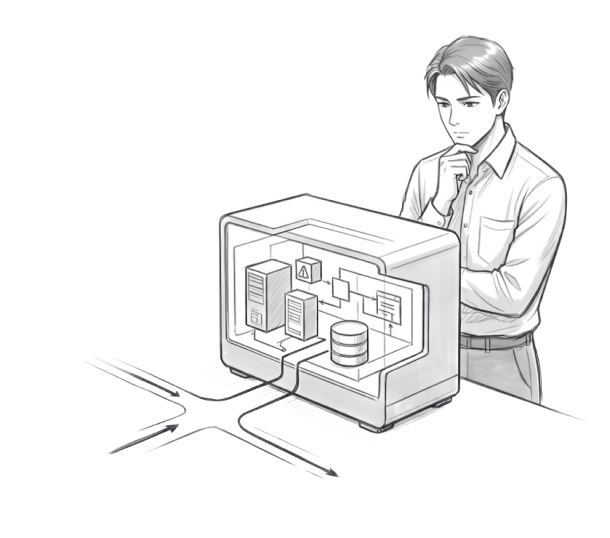
Threat Actor Misdirection
For organisations protecting high-value assets
A micro-network of believable decoys sits alongside your real infrastructure, drawing attackers away from critical systems. While they explore what looks like a legitimate environment, your actual assets remain untouched and your team gains valuable time to respond.
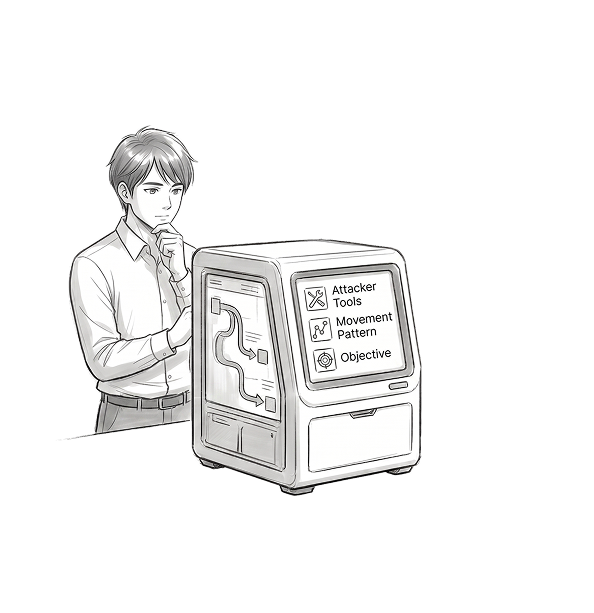
Actionable Threat Intelligence
Every move an attacker makes inside the deception environment is recorded – their tools, techniques, lateral movement patterns, and objectives. That intelligence feeds directly back into your defences, strengthening detection rules and closing the gaps that the attacker was specifically trying to exploit.
VDI Dependency reduction
CVSS > = 4.0 findings
Public sensitive data reduction
Why engage Nayaka for next-gen honeypots?
Deception technology is only effective when decoys are convincing, well-placed, and tuned to your specific environment. A generic deployment gets ignored by experienced attackers. Nayaka works with you to design a deception strategy that fits your infrastructure, then matches it to the right platform from our partner ecosystem – supporting you from initial design through to live intelligence collection.
Scope Definition:
Which assets to protect, where decoys should sit, and what attacker behaviour to prioritise.
Vendor Alignment
Best-fit deception platform matched to your environment and threat profile.
boarding and integration:
Decoy deployment connected to your SIEM and response workflows.
Operationalisation:
Turning attacker interactions into actionable intelligence that actively strengthens your defences.

Scope your Deception Programme with Nayaka
Asset Discovery
Map your environment to identify the high-value assets, network segments, and access paths that represent the most attractive targets - and where strategically placed decoys will intercept attackers most effectively.
Establish Goals
Define whether the priority is early intrusion detection, lateral movement visibility, threat intelligence collection, or protecting a specific set of critical assets from targeted attack.
DETERMINE RoE
Agree on decoy placement, how attacker interactions are escalated, what automated responses are permitted, and how intelligence feeds back into your wider security operations before going live.
Tell us what you are most concerned about – whether that is lateral movement going undetected, targeted attacks on specific assets, or simply having no visibility once an attacker is inside your perimeter. We will identify the right deception approach within our partner ecosystem and connect you to the right people, without unnecessary complexity.
Will legitimate users accidentally trigger the honeypots?
No. Decoys are placed in locations and configurations that no legitimate user would ever have reason to access. Any interaction is an immediate, unambiguous signal of malicious activity – which is what makes deception-based detection so accurate.
How realistic do the decoys need to be to fool experienced attackers?
Very realistic. The platforms we work with use narrative-driven environments that mirror genuine infrastructure – including believable credentials, file structures, and service behaviour – specifically designed to deceive skilled human attackers, not just automated tools.
Does it work alongside our existing detection tools?
Yes. Next-gen honeypots complement your existing SIEM, EDR, and network monitoring by adding a layer of deception-based detection that generates high-confidence, low-noise alerts — enhancing your overall detection capability rather than replacing any existing tool.
How do we get started?
Share your current environment, the assets you most want to protect, and your biggest detection blind spots. We will run a scoping call and arrange a demo that shows exactly how decoys would be positioned within your specific infrastructure.