ADVANCED THREAT DETECTION
Manage XDR deliveries with advanced threat detection across multiple vectors, providing broader protection against evolving risks.
Detect, investigate, and respond to threats across your entire environment – endpoints, cloud, network, and identity 8 without building an in-house SOC. Managed XDR gives you 24/7 expert-backed protection that scales with your organisation.
Advanced threat detection across multiple vectors
Continuous monitoring and rapid incident response
Integrated security management in one platform
Comprehensive threat detection and
response, backed by expert support
Siloed security tools generate fragmented alerts that no single analyst can piece together in time. Attackers move laterally across your environment while your team is still triaging the first notification. Managed XDR changes that dynamic by correlating signals from every layer of your infrastructure – endpoint, email, cloud workloads, identity, and network traffic – into a single, continuously monitored picture. Threats are identified faster, investigated more thoroughly, and contained before they escalate into incidents.
Nayaka helps mid-size organisations select and deploy the right Managed XDR platform from our partner ecosystem, with expert guidance from initial scoping through to full operational handover.
Integrated Security Management
For lean security and IT teams
Disconnected tools slow your team down. Managed XDR unifies endpoint, cloud, network, and identity telemetry into a single interface -so threats are investigated and contained from one place, not pieced together across multiple consoles.
Proactive Threat Detection
Alerts tell you something already happened. Expert analysts go further – actively hunting for signs of lateral movement, credential abuse, and hidden persistence before they develop into a breach.
VDI Dependency reduction
CVSS > = 4.0 findings
Public sensitive data reduction
Why engage Nayaka for Managed XDR?
Selecting a Managed XDR provider is one of the most consequential security decisions an organisation can make. The wrong fit means missed detections, alert fatigue, and a service that never fully understands your environment. Nayaka maps your infrastructure, team size, and risk profile against our partner ecosystem to find the right platform – then supports the entire journey from commercial alignment to day-one operations.
Scope Definition:
Which environments to cover, detection priorities, and response boundaries.
Vendor Alignment
Right-fit Managed XDR platform matched to your stack and team capacity.
boarding and integration:
Connecting telemetry from endpoints, cloud, identity, and network into a unified service
Operationalisation:
Moving from first detections to measurable reduction in dwell time and incident impact.

Scope your Managed XDR Programme with Nayaka
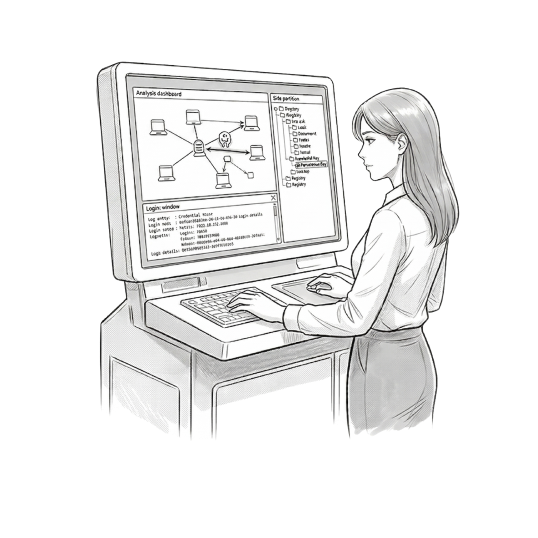
Asset Discovery
Inventory your environment: endpoints, cloud workloads, identity providers, network segments, and existing security tooling - to establish what needs to feed into the XDR platform and where current visibility gaps sit.
Establish Goals
Define whether the priority is faster detection, improved incident response, compliance evidence, or all three - and align on the response actions the provider is authorised to take on your behalf.
DETERMINE RoE
Agree on escalation paths, containment authorities, communication protocols, and SLA expectations before the service goes live - so your team and the provider operate as one when an incident hits.
Tell us what keeps you up at night – whether that is ransomware, insider threats, cloud misconfiguration, or simply not knowing what is happening across your environment right now. We will identify the most appropriate Managed XDR approach within our partner ecosystem and put you in front of the right people, quickly and without unnecessary complexity.
Is Managed XDR a replacement for our existing security tools?
It is designed to sit on top of your existing stack, not replace it. Managed XDR ingests telemetry from your current tools and correlates it centrally – so your existing investments are enhanced rather than discarded.
How quickly can Managed XDR be deployed?
Initial onboarding typically takes two to four weeks depending on environment complexity. The platform begins detecting and alerting from day one, with tuning improving fidelity over the first few weeks as baselines are established.
What happens when a threat is detected?
Analysts investigate the alert, validate the threat, and either contain it directly – if response authorities have been agreed in advance – or escalate to your team with clear remediation guidance. Response speed depends on the severity tier and agreed rules of engagement.
How do we get started?
Share your current environment, team size, and the threats you are most concerned about. We will run a scoping call, align on coverage requirements, and arrange a tailored demo with the most suitable provider in our ecosystem.